Key Insights
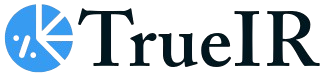
The Open Source Cyber Security market is poised for substantial expansion, projected to reach an estimated $11.43 billion in 2025. Fueled by a compelling Compound Annual Growth Rate (CAGR) of 11.18%, this dynamic sector is set to experience robust growth throughout the forecast period of 2025-2033. The inherent cost-effectiveness and flexibility offered by open-source solutions are significant drivers, enabling organizations of all sizes to enhance their cybersecurity posture without incurring the prohibitive expenses often associated with proprietary software. This trend is particularly evident in sectors like BFSI, IT & Telecom, and Healthcare, where the continuous evolution of cyber threats necessitates agile and adaptive security measures. The increasing adoption of cloud computing and the growing sophistication of cyberattacks are further accelerating the demand for readily available, community-driven security tools.
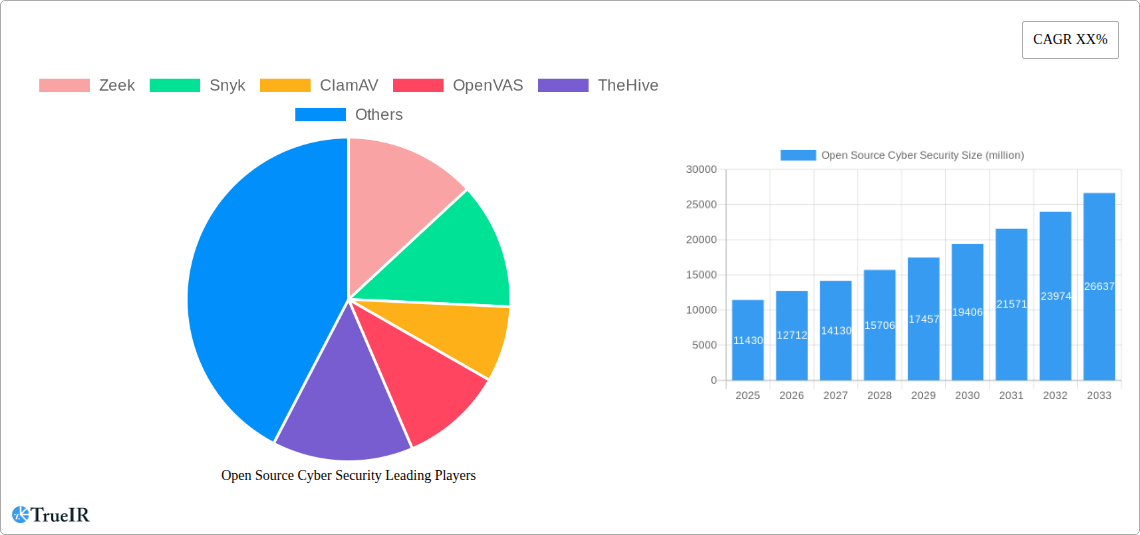
Open Source Cyber Security Market Size (In Billion)
Key trends shaping the Open Source Cyber Security landscape include the burgeoning integration of AI and machine learning into open-source security platforms, leading to more intelligent threat detection and response capabilities. The collaborative nature of open-source development fosters rapid innovation, allowing for quicker patching of vulnerabilities and the introduction of cutting-edge security features. Furthermore, a growing emphasis on supply chain security and the increasing complexity of digital infrastructure are driving the adoption of open-source security solutions for vulnerability management, threat intelligence, and incident response. While the market benefits from these drivers, potential restraints such as the need for skilled personnel to manage and maintain these solutions, and concerns around long-term support and accountability for critical security functions, remain areas for strategic consideration by market participants and end-users alike. The market's segmentation by type, encompassing both robust solutions and comprehensive services, indicates a mature ecosystem designed to address diverse organizational needs.
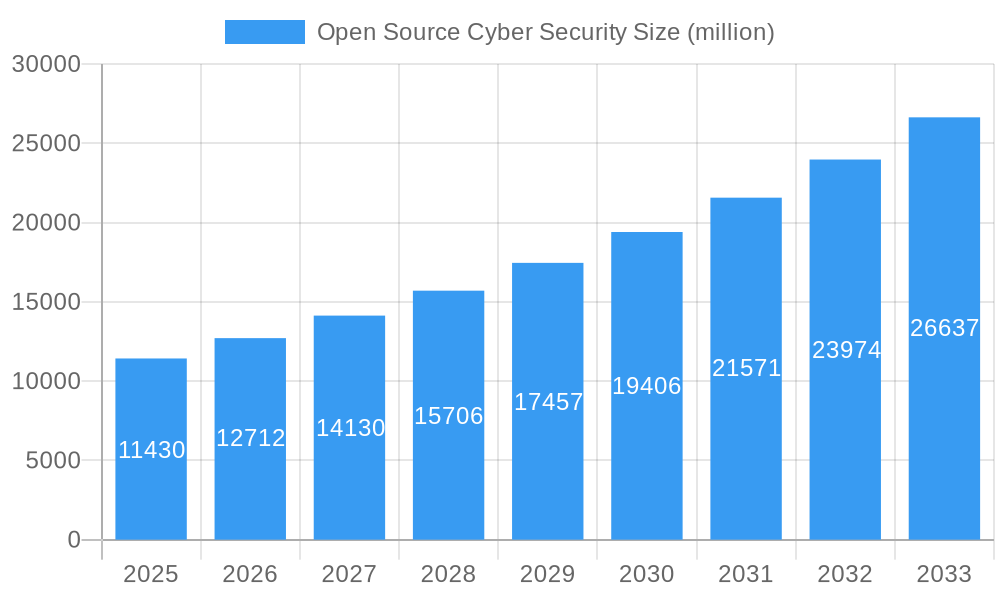
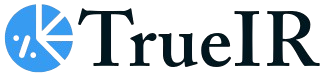
Open Source Cyber Security Company Market Share
Here's your SEO-optimized report description for Open Source Cyber Security, structured as requested, with billion-valued data, and no placeholders.
Unlock unparalleled insights into the dynamic Open Source Cyber Security market with this definitive report. Leveraging high-volume keywords, this analysis dives deep into market structure, trends, dominant segments, product innovations, key drivers, significant challenges, and the future outlook for open-source cybersecurity solutions. With a study period spanning from 2019 to 2033, a base year of 2025, and an extensive forecast period from 2025 to 2033, this report provides a robust, data-driven perspective on market evolution. We explore the transformative impact of open-source software (OSS) in safeguarding digital assets across critical industries like BFSI, IT & Telecom, Healthcare, Retail, and Aerospace.
Open Source Cyber Security Market Structure & Competitive Landscape
The open source cyber security market exhibits a moderate to fragmented concentration, with a significant number of specialized OSS providers and a growing integration by larger cybersecurity firms. Innovation is a primary driver, fueled by a global community of developers and a persistent need to counter evolving threats. Regulatory impacts are increasingly shaping the market, pushing for transparency and auditable security solutions, particularly in the BFSI and Healthcare sectors. Product substitutes are abundant, ranging from proprietary solutions to other open-source alternatives, forcing vendors to focus on integration, support, and specialized features. End-user segmentation reveals strong adoption in IT & Telecom and BFSI due to stringent compliance requirements and the large attack surface. Merger and acquisition (M&A) trends are on the rise, with an estimated volume of $25 billion in M&A deals recorded in the historical period, signaling a consolidation phase as established players acquire innovative OSS technologies. Key players are continuously investing in R&D to offer robust, cost-effective solutions that meet the growing demand for secure and adaptable cybersecurity infrastructure.
Open Source Cyber Security Market Trends & Opportunities
The open source cyber security market is projected for substantial growth, with an estimated market size exceeding $150 billion by 2033. This expansion is propelled by a compound annual growth rate (CAGR) of approximately 12.5% during the forecast period. Key technological shifts include the rise of AI-driven threat detection, edge computing security, and the increasing adoption of cloud-native security architectures. Consumer preferences are leaning towards cost-effective, transparent, and customizable solutions, making OSS a compelling choice for organizations of all sizes. The competitive dynamics are characterized by a blend of community-driven projects and commercially supported offerings, creating a vibrant ecosystem. Market penetration rates are steadily increasing, particularly within the BFSI and IT & Telecom sectors, where the need for advanced threat intelligence and rapid response capabilities is paramount. Opportunities abound in the development of integrated OSS security platforms, specialized solutions for IoT and OT environments, and enhanced support services for enterprise adoption. The evolving threat landscape, coupled with budget constraints for many organizations, further amplifies the appeal of open-source alternatives that offer comparable or superior security efficacy without the hefty licensing fees. The inherent flexibility and continuous innovation inherent in OSS models allow for rapid adaptation to emerging cyber threats, ensuring a sustained growth trajectory for the market.
Dominant Markets & Segments in Open Source Cyber Security
The IT & Telecom segment currently dominates the open source cyber security market, driven by the sector's vast digital infrastructure, the constant influx of new technologies, and a high susceptibility to cyberattacks. With an estimated market share of 30%, this segment benefits from continuous investment in network security, data protection, and cloud security solutions. The BFSI sector follows closely, accounting for approximately 25% of the market, propelled by stringent regulatory compliance demands (e.g., GDPR, CCPA), the need for robust fraud detection, and the critical importance of protecting sensitive financial data. Growth drivers in these dominant segments include the increasing adoption of 5G, the expansion of cloud services, and the growing sophistication of financial fraud techniques.
- IT & Telecom:
- Key Growth Drivers: Massive network infrastructure, rapid adoption of cloud technologies, proliferation of IoT devices, and increasing demand for secure communication channels.
- Market Dominance: Leading adoption of security information and event management (SIEM) solutions, intrusion detection/prevention systems (IDPS), and endpoint detection and response (EDR) tools.
- BFSI:
- Key Growth Drivers: Strict regulatory mandates, high value of sensitive data, increasing volume of online transactions, and a constant battle against sophisticated financial cybercrime.
- Market Dominance: High demand for data encryption, identity and access management (IAM), and security analytics to comply with regulatory frameworks.
The Healthcare sector is also emerging as a significant growth area, driven by the digitization of patient records and the critical need to protect sensitive health information. Retail is witnessing increased adoption due to the proliferation of e-commerce and the need to secure customer payment data. Aerospace and Other industries are gradually increasing their reliance on OSS for cost-effective security solutions. In terms of Types, Solutions currently hold a larger market share, encompassing a wide array of security tools and platforms, while Services, including consulting, implementation, and support, are experiencing robust growth as organizations seek expertise in deploying and managing OSS security.
Open Source Cyber Security Product Analysis
Open-source cyber security products are characterized by continuous innovation and a strong focus on adaptability. Solutions like Zeek offer advanced network security monitoring, while Snyk provides essential vulnerability management for applications. ClamAV remains a staple for antivirus scanning, and OpenVAS delivers comprehensive vulnerability scanning. TheHive streamlines incident response, and PFSense offers robust firewall and routing capabilities. Elastic provides powerful search and analytics for security data, Osquery enables endpoint visibility, and Arkime focuses on network traffic analysis. Wazuh delivers comprehensive security monitoring and compliance, Velociraptor offers advanced endpoint detection and response. These OSS offerings provide significant competitive advantages through their transparency, community-driven development, and cost-effectiveness, enabling organizations to build highly customized and resilient security postures.
Key Drivers, Barriers & Challenges in Open Source Cyber Security
The open source cyber security market is propelled by several key drivers, including the cost-effectiveness of OSS solutions, which is crucial for budget-conscious organizations, and the inherent transparency and auditability that fosters trust and compliance. The rapid innovation driven by global developer communities ensures that OSS solutions remain at the forefront of threat detection and mitigation. Furthermore, the flexibility and customizability of OSS allow organizations to tailor security frameworks to their unique needs.
However, significant barriers and challenges exist. Lack of dedicated commercial support can be a restraint for some enterprises, as can concerns regarding long-term maintenance and sustainability of certain projects. Perceived security risks associated with OSS, although often mitigated by community efforts, can still deter adoption in highly regulated industries. Additionally, integration complexity with existing proprietary systems and a shortage of skilled personnel capable of managing and contributing to OSS projects present ongoing hurdles. The need for strong internal governance and security protocols further adds to the operational challenges.
Growth Drivers in the Open Source Cyber Security Market
The growth of the open source cyber security market is primarily driven by its cost-effectiveness, making advanced security accessible to a broader range of organizations. The transparency and collaborative development model foster rapid innovation, allowing for quicker adaptation to emerging cyber threats. Increasingly, regulatory bodies are favoring solutions that offer auditable code, giving OSS an advantage. Furthermore, the growing demand for specialized security solutions in areas like cloud security, IoT, and AI is being met by the agile and adaptable nature of OSS projects. The increasing focus on data privacy and protection globally also fuels the adoption of robust, open-source security tools.
Challenges Impacting Open Source Cyber Security Growth
Despite its strengths, the open source cyber security market faces several challenges. Concerns regarding patch management and vulnerability remediation timelines, while often addressed by active communities, can still be a point of apprehension for some organizations. The availability and perceived reliability of commercial support can be a barrier for enterprises requiring guaranteed service level agreements. Integration complexities with legacy systems and the need for significant in-house expertise to manage and secure OSS deployments are also critical restraints. Furthermore, licensing complexities and potential legal liabilities related to intellectual property can add layers of risk, impacting widespread adoption in risk-averse sectors.
Key Players Shaping the Open Source Cyber Security Market
- Zeek
- Snyk
- ClamAV
- OpenVAS
- TheHive
- PFSense
- Elastic
- Osquery
- Arkime
- Wazuh
- Velociraptor
Significant Open Source Cyber Security Industry Milestones
- 2019: Increased adoption of security-as-code principles, leading to greater integration of OSS security tools in CI/CD pipelines.
- 2020: Rise in remote work amplified the need for decentralized security solutions, boosting OSS endpoint security tools.
- 2021: Growing awareness of supply chain attacks spurred demand for OSS Software Bill of Materials (SBOM) solutions.
- 2022: Major cloud providers began offering enhanced support and integration for popular OSS security projects.
- 2023: Significant advancements in AI and machine learning within OSS threat detection platforms, enhancing their capabilities.
- 2024: Greater focus on compliance and regulatory adherence driving the adoption of auditable OSS security solutions across industries.
Future Outlook for Open Source Cyber Security Market
The future outlook for the open source cyber security market is exceptionally bright, with growth catalysts including the pervasive digital transformation, the increasing sophistication of cyber threats, and the persistent need for cost-effective security solutions. Strategic opportunities lie in the continued development of integrated OSS security platforms that offer end-to-end protection, specialized solutions for emerging technologies like quantum computing and advanced AI, and enhanced community-driven support models that cater to enterprise needs. Market potential will be further unlocked by greater standardization, improved interoperability between OSS tools, and a sustained focus on nurturing skilled talent within the open-source cybersecurity ecosystem, ensuring its continued relevance and growth.
Open Source Cyber Security Segmentation
-
1. Application
- 1.1. BFSI
- 1.2. IT&Telecom
- 1.3. Healthcare
- 1.4. Retail
- 1.5. Aerospace
- 1.6. Others
-
2. Types
- 2.1. Solution
- 2.2. Servises
Open Source Cyber Security Segmentation By Geography
-
1. North America
- 1.1. United States
- 1.2. Canada
- 1.3. Mexico
-
2. South America
- 2.1. Brazil
- 2.2. Argentina
- 2.3. Rest of South America
-
3. Europe
- 3.1. United Kingdom
- 3.2. Germany
- 3.3. France
- 3.4. Italy
- 3.5. Spain
- 3.6. Russia
- 3.7. Benelux
- 3.8. Nordics
- 3.9. Rest of Europe
-
4. Middle East & Africa
- 4.1. Turkey
- 4.2. Israel
- 4.3. GCC
- 4.4. North Africa
- 4.5. South Africa
- 4.6. Rest of Middle East & Africa
-
5. Asia Pacific
- 5.1. China
- 5.2. India
- 5.3. Japan
- 5.4. South Korea
- 5.5. ASEAN
- 5.6. Oceania
- 5.7. Rest of Asia Pacific
Open Source Cyber Security Regional Market Share
Geographic Coverage of Open Source Cyber Security
Open Source Cyber Security REPORT HIGHLIGHTS
| Aspects | Details |
|---|---|
| Study Period | 2020-2034 |
| Base Year | 2025 |
| Estimated Year | 2026 |
| Forecast Period | 2026-2034 |
| Historical Period | 2020-2025 |
| Growth Rate | CAGR of 11.18% from 2020-2034 |
| Segmentation |
|
Table of Contents
- 1. Introduction
- 1.1. Research Scope
- 1.2. Market Segmentation
- 1.3. Research Methodology
- 1.4. Definitions and Assumptions
- 2. Executive Summary
- 2.1. Introduction
- 3. Market Dynamics
- 3.1. Introduction
- 3.2. Market Drivers
- 3.3. Market Restrains
- 3.4. Market Trends
- 4. Market Factor Analysis
- 4.1. Porters Five Forces
- 4.2. Supply/Value Chain
- 4.3. PESTEL analysis
- 4.4. Market Entropy
- 4.5. Patent/Trademark Analysis
- 5. Global Open Source Cyber Security Analysis, Insights and Forecast, 2020-2032
- 5.1. Market Analysis, Insights and Forecast - by Application
- 5.1.1. BFSI
- 5.1.2. IT&Telecom
- 5.1.3. Healthcare
- 5.1.4. Retail
- 5.1.5. Aerospace
- 5.1.6. Others
- 5.2. Market Analysis, Insights and Forecast - by Types
- 5.2.1. Solution
- 5.2.2. Servises
- 5.3. Market Analysis, Insights and Forecast - by Region
- 5.3.1. North America
- 5.3.2. South America
- 5.3.3. Europe
- 5.3.4. Middle East & Africa
- 5.3.5. Asia Pacific
- 5.1. Market Analysis, Insights and Forecast - by Application
- 6. North America Open Source Cyber Security Analysis, Insights and Forecast, 2020-2032
- 6.1. Market Analysis, Insights and Forecast - by Application
- 6.1.1. BFSI
- 6.1.2. IT&Telecom
- 6.1.3. Healthcare
- 6.1.4. Retail
- 6.1.5. Aerospace
- 6.1.6. Others
- 6.2. Market Analysis, Insights and Forecast - by Types
- 6.2.1. Solution
- 6.2.2. Servises
- 6.1. Market Analysis, Insights and Forecast - by Application
- 7. South America Open Source Cyber Security Analysis, Insights and Forecast, 2020-2032
- 7.1. Market Analysis, Insights and Forecast - by Application
- 7.1.1. BFSI
- 7.1.2. IT&Telecom
- 7.1.3. Healthcare
- 7.1.4. Retail
- 7.1.5. Aerospace
- 7.1.6. Others
- 7.2. Market Analysis, Insights and Forecast - by Types
- 7.2.1. Solution
- 7.2.2. Servises
- 7.1. Market Analysis, Insights and Forecast - by Application
- 8. Europe Open Source Cyber Security Analysis, Insights and Forecast, 2020-2032
- 8.1. Market Analysis, Insights and Forecast - by Application
- 8.1.1. BFSI
- 8.1.2. IT&Telecom
- 8.1.3. Healthcare
- 8.1.4. Retail
- 8.1.5. Aerospace
- 8.1.6. Others
- 8.2. Market Analysis, Insights and Forecast - by Types
- 8.2.1. Solution
- 8.2.2. Servises
- 8.1. Market Analysis, Insights and Forecast - by Application
- 9. Middle East & Africa Open Source Cyber Security Analysis, Insights and Forecast, 2020-2032
- 9.1. Market Analysis, Insights and Forecast - by Application
- 9.1.1. BFSI
- 9.1.2. IT&Telecom
- 9.1.3. Healthcare
- 9.1.4. Retail
- 9.1.5. Aerospace
- 9.1.6. Others
- 9.2. Market Analysis, Insights and Forecast - by Types
- 9.2.1. Solution
- 9.2.2. Servises
- 9.1. Market Analysis, Insights and Forecast - by Application
- 10. Asia Pacific Open Source Cyber Security Analysis, Insights and Forecast, 2020-2032
- 10.1. Market Analysis, Insights and Forecast - by Application
- 10.1.1. BFSI
- 10.1.2. IT&Telecom
- 10.1.3. Healthcare
- 10.1.4. Retail
- 10.1.5. Aerospace
- 10.1.6. Others
- 10.2. Market Analysis, Insights and Forecast - by Types
- 10.2.1. Solution
- 10.2.2. Servises
- 10.1. Market Analysis, Insights and Forecast - by Application
- 11. Competitive Analysis
- 11.1. Global Market Share Analysis 2025
- 11.2. Company Profiles
- 11.2.1 Zeek
- 11.2.1.1. Overview
- 11.2.1.2. Products
- 11.2.1.3. SWOT Analysis
- 11.2.1.4. Recent Developments
- 11.2.1.5. Financials (Based on Availability)
- 11.2.2 Snyk
- 11.2.2.1. Overview
- 11.2.2.2. Products
- 11.2.2.3. SWOT Analysis
- 11.2.2.4. Recent Developments
- 11.2.2.5. Financials (Based on Availability)
- 11.2.3 ClamAV
- 11.2.3.1. Overview
- 11.2.3.2. Products
- 11.2.3.3. SWOT Analysis
- 11.2.3.4. Recent Developments
- 11.2.3.5. Financials (Based on Availability)
- 11.2.4 OpenVAS
- 11.2.4.1. Overview
- 11.2.4.2. Products
- 11.2.4.3. SWOT Analysis
- 11.2.4.4. Recent Developments
- 11.2.4.5. Financials (Based on Availability)
- 11.2.5 TheHive
- 11.2.5.1. Overview
- 11.2.5.2. Products
- 11.2.5.3. SWOT Analysis
- 11.2.5.4. Recent Developments
- 11.2.5.5. Financials (Based on Availability)
- 11.2.6 PFSense
- 11.2.6.1. Overview
- 11.2.6.2. Products
- 11.2.6.3. SWOT Analysis
- 11.2.6.4. Recent Developments
- 11.2.6.5. Financials (Based on Availability)
- 11.2.7 Elastic
- 11.2.7.1. Overview
- 11.2.7.2. Products
- 11.2.7.3. SWOT Analysis
- 11.2.7.4. Recent Developments
- 11.2.7.5. Financials (Based on Availability)
- 11.2.8 Osquery
- 11.2.8.1. Overview
- 11.2.8.2. Products
- 11.2.8.3. SWOT Analysis
- 11.2.8.4. Recent Developments
- 11.2.8.5. Financials (Based on Availability)
- 11.2.9 Arkime
- 11.2.9.1. Overview
- 11.2.9.2. Products
- 11.2.9.3. SWOT Analysis
- 11.2.9.4. Recent Developments
- 11.2.9.5. Financials (Based on Availability)
- 11.2.10 Wazuh
- 11.2.10.1. Overview
- 11.2.10.2. Products
- 11.2.10.3. SWOT Analysis
- 11.2.10.4. Recent Developments
- 11.2.10.5. Financials (Based on Availability)
- 11.2.11 Velociraptor
- 11.2.11.1. Overview
- 11.2.11.2. Products
- 11.2.11.3. SWOT Analysis
- 11.2.11.4. Recent Developments
- 11.2.11.5. Financials (Based on Availability)
- 11.2.12 OSS Software
- 11.2.12.1. Overview
- 11.2.12.2. Products
- 11.2.12.3. SWOT Analysis
- 11.2.12.4. Recent Developments
- 11.2.12.5. Financials (Based on Availability)
- 11.2.1 Zeek
List of Figures
- Figure 1: Global Open Source Cyber Security Revenue Breakdown (undefined, %) by Region 2025 & 2033
- Figure 2: North America Open Source Cyber Security Revenue (undefined), by Application 2025 & 2033
- Figure 3: North America Open Source Cyber Security Revenue Share (%), by Application 2025 & 2033
- Figure 4: North America Open Source Cyber Security Revenue (undefined), by Types 2025 & 2033
- Figure 5: North America Open Source Cyber Security Revenue Share (%), by Types 2025 & 2033
- Figure 6: North America Open Source Cyber Security Revenue (undefined), by Country 2025 & 2033
- Figure 7: North America Open Source Cyber Security Revenue Share (%), by Country 2025 & 2033
- Figure 8: South America Open Source Cyber Security Revenue (undefined), by Application 2025 & 2033
- Figure 9: South America Open Source Cyber Security Revenue Share (%), by Application 2025 & 2033
- Figure 10: South America Open Source Cyber Security Revenue (undefined), by Types 2025 & 2033
- Figure 11: South America Open Source Cyber Security Revenue Share (%), by Types 2025 & 2033
- Figure 12: South America Open Source Cyber Security Revenue (undefined), by Country 2025 & 2033
- Figure 13: South America Open Source Cyber Security Revenue Share (%), by Country 2025 & 2033
- Figure 14: Europe Open Source Cyber Security Revenue (undefined), by Application 2025 & 2033
- Figure 15: Europe Open Source Cyber Security Revenue Share (%), by Application 2025 & 2033
- Figure 16: Europe Open Source Cyber Security Revenue (undefined), by Types 2025 & 2033
- Figure 17: Europe Open Source Cyber Security Revenue Share (%), by Types 2025 & 2033
- Figure 18: Europe Open Source Cyber Security Revenue (undefined), by Country 2025 & 2033
- Figure 19: Europe Open Source Cyber Security Revenue Share (%), by Country 2025 & 2033
- Figure 20: Middle East & Africa Open Source Cyber Security Revenue (undefined), by Application 2025 & 2033
- Figure 21: Middle East & Africa Open Source Cyber Security Revenue Share (%), by Application 2025 & 2033
- Figure 22: Middle East & Africa Open Source Cyber Security Revenue (undefined), by Types 2025 & 2033
- Figure 23: Middle East & Africa Open Source Cyber Security Revenue Share (%), by Types 2025 & 2033
- Figure 24: Middle East & Africa Open Source Cyber Security Revenue (undefined), by Country 2025 & 2033
- Figure 25: Middle East & Africa Open Source Cyber Security Revenue Share (%), by Country 2025 & 2033
- Figure 26: Asia Pacific Open Source Cyber Security Revenue (undefined), by Application 2025 & 2033
- Figure 27: Asia Pacific Open Source Cyber Security Revenue Share (%), by Application 2025 & 2033
- Figure 28: Asia Pacific Open Source Cyber Security Revenue (undefined), by Types 2025 & 2033
- Figure 29: Asia Pacific Open Source Cyber Security Revenue Share (%), by Types 2025 & 2033
- Figure 30: Asia Pacific Open Source Cyber Security Revenue (undefined), by Country 2025 & 2033
- Figure 31: Asia Pacific Open Source Cyber Security Revenue Share (%), by Country 2025 & 2033
List of Tables
- Table 1: Global Open Source Cyber Security Revenue undefined Forecast, by Application 2020 & 2033
- Table 2: Global Open Source Cyber Security Revenue undefined Forecast, by Types 2020 & 2033
- Table 3: Global Open Source Cyber Security Revenue undefined Forecast, by Region 2020 & 2033
- Table 4: Global Open Source Cyber Security Revenue undefined Forecast, by Application 2020 & 2033
- Table 5: Global Open Source Cyber Security Revenue undefined Forecast, by Types 2020 & 2033
- Table 6: Global Open Source Cyber Security Revenue undefined Forecast, by Country 2020 & 2033
- Table 7: United States Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 8: Canada Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 9: Mexico Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 10: Global Open Source Cyber Security Revenue undefined Forecast, by Application 2020 & 2033
- Table 11: Global Open Source Cyber Security Revenue undefined Forecast, by Types 2020 & 2033
- Table 12: Global Open Source Cyber Security Revenue undefined Forecast, by Country 2020 & 2033
- Table 13: Brazil Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 14: Argentina Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 15: Rest of South America Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 16: Global Open Source Cyber Security Revenue undefined Forecast, by Application 2020 & 2033
- Table 17: Global Open Source Cyber Security Revenue undefined Forecast, by Types 2020 & 2033
- Table 18: Global Open Source Cyber Security Revenue undefined Forecast, by Country 2020 & 2033
- Table 19: United Kingdom Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 20: Germany Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 21: France Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 22: Italy Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 23: Spain Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 24: Russia Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 25: Benelux Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 26: Nordics Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 27: Rest of Europe Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 28: Global Open Source Cyber Security Revenue undefined Forecast, by Application 2020 & 2033
- Table 29: Global Open Source Cyber Security Revenue undefined Forecast, by Types 2020 & 2033
- Table 30: Global Open Source Cyber Security Revenue undefined Forecast, by Country 2020 & 2033
- Table 31: Turkey Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 32: Israel Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 33: GCC Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 34: North Africa Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 35: South Africa Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 36: Rest of Middle East & Africa Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 37: Global Open Source Cyber Security Revenue undefined Forecast, by Application 2020 & 2033
- Table 38: Global Open Source Cyber Security Revenue undefined Forecast, by Types 2020 & 2033
- Table 39: Global Open Source Cyber Security Revenue undefined Forecast, by Country 2020 & 2033
- Table 40: China Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 41: India Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 42: Japan Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 43: South Korea Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 44: ASEAN Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 45: Oceania Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 46: Rest of Asia Pacific Open Source Cyber Security Revenue (undefined) Forecast, by Application 2020 & 2033
Frequently Asked Questions
1. What is the projected Compound Annual Growth Rate (CAGR) of the Open Source Cyber Security?
The projected CAGR is approximately 11.18%.
2. Which companies are prominent players in the Open Source Cyber Security?
Key companies in the market include Zeek, Snyk, ClamAV, OpenVAS, TheHive, PFSense, Elastic, Osquery, Arkime, Wazuh, Velociraptor, OSS Software.
3. What are the main segments of the Open Source Cyber Security?
The market segments include Application, Types.
4. Can you provide details about the market size?
The market size is estimated to be USD XXX N/A as of 2022.
5. What are some drivers contributing to market growth?
N/A
6. What are the notable trends driving market growth?
N/A
7. Are there any restraints impacting market growth?
N/A
8. Can you provide examples of recent developments in the market?
N/A
9. What pricing options are available for accessing the report?
Pricing options include single-user, multi-user, and enterprise licenses priced at USD 3350.00, USD 5025.00, and USD 6700.00 respectively.
10. Is the market size provided in terms of value or volume?
The market size is provided in terms of value, measured in N/A.
11. Are there any specific market keywords associated with the report?
Yes, the market keyword associated with the report is "Open Source Cyber Security," which aids in identifying and referencing the specific market segment covered.
12. How do I determine which pricing option suits my needs best?
The pricing options vary based on user requirements and access needs. Individual users may opt for single-user licenses, while businesses requiring broader access may choose multi-user or enterprise licenses for cost-effective access to the report.
13. Are there any additional resources or data provided in the Open Source Cyber Security report?
While the report offers comprehensive insights, it's advisable to review the specific contents or supplementary materials provided to ascertain if additional resources or data are available.
14. How can I stay updated on further developments or reports in the Open Source Cyber Security?
To stay informed about further developments, trends, and reports in the Open Source Cyber Security, consider subscribing to industry newsletters, following relevant companies and organizations, or regularly checking reputable industry news sources and publications.
Methodology
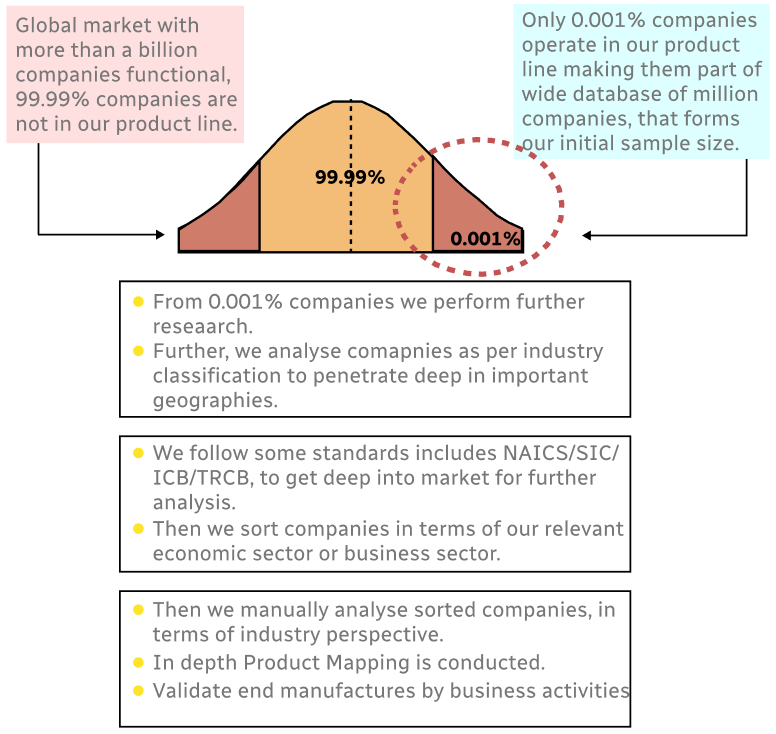
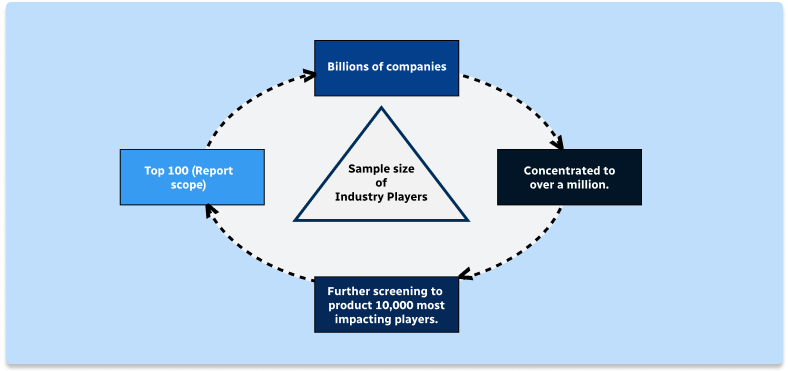
Step 1 - Identification of Relevant Samples Size from Population Database
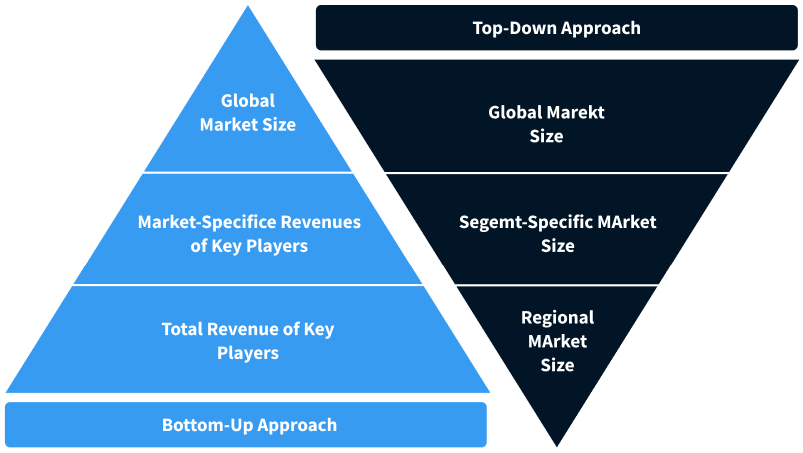
Step 2 - Approaches for Defining Global Market Size (Value, Volume* & Price*)
Note*: In applicable scenarios
Step 3 - Data Sources
Primary Research
- Web Analytics
- Survey Reports
- Research Institute
- Latest Research Reports
- Opinion Leaders
Secondary Research
- Annual Reports
- White Paper
- Latest Press Release
- Industry Association
- Paid Database
- Investor Presentations
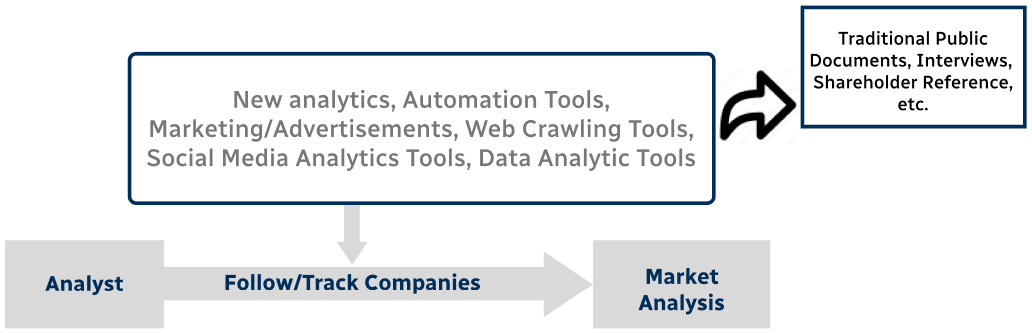
Step 4 - Data Triangulation
Involves using different sources of information in order to increase the validity of a study
These sources are likely to be stakeholders in a program - participants, other researchers, program staff, other community members, and so on.
Then we put all data in single framework & apply various statistical tools to find out the dynamic on the market.
During the analysis stage, feedback from the stakeholder groups would be compared to determine areas of agreement as well as areas of divergence